ISO IEC 27001-2022-AMD1-2024
VIP免费
INTERNATIONAL ISO/IEC
STANDARD 27001
Third edition
2022-10
Information security,cybersecurity
and privacy protection—Information
security management systems—
Requirements
Sécurité de I'information,cybersécurité etprotection de la vie
privée —Systèmes de management de la sécurité de I'information —
Exigences
Reference number
ISO/IEC27001:2022(E)
OISO/IEC 2022
ISO/IEC 27001:2022(E)
COPYRIGHT PROTECTED DOCUMENT
O ISO/IEC2022
All rights reserved.Unless otherwise specified,or required in the context ofits implementation,no part of this publication may
be reproduced or utilized otherwise in any form or by any means,electronic or mechanical,including photocopying,or posting on
the internet or an intranet,without prior writen permission.Permission can be requested from either ISO afthe address below
or ISO's member body in the country of the requester.
ISO copyright office
CP401·Ch.de Blandonnet 8
CH-1214 Vernier,Geneva
Phone:+41227490111
Email:copyright@iso.org
Website:wwwiso.org
Published in Switzerland
ii O ISO/IEC 2022-All rights reserved
ISO/IEC27001:2022(E)
Contents Page
Foreword ...................................................................................................................................................... iv
Introduction .................................................................................................................................................. V
1 Scope .................................................................................................................................................. 1
2 Normative references ................................................................................................................... 1
3 Terms and definitions ..................................................................................................................... 1
4 Context of the organization .......................................................................................................... 1
4.1 Understanding the organization and its context .............................................................. 1
4.2 Understanding the needs and expectations of interested parties ...................................1
4.3 Determining the scope of the information security management system ......................2
4.4 Information security management system ....................................................................... 2
5 Leadership ....................................................................................................................................... 2
5.1 Leadership and commitment ..............................................................................................2
5.2 Policy .......................................................................................................................................3
5.3 Organizational roles,responsibilities and authorities ................................................... 3
6 Planning ........................................................................................................................................... 3
6.1 Actions to address risks and opportunities ......................................................................3
6.1.1 General ......................................................................................................................3
6.1.2 Information security risk assessment ................................................................... 4
6.1.3 Information security risk treatment ................................................................... 4
6.2 Information security objectives and planning to achieve them ...................................... 5
7Support ........................................................................................................................................... 6
7.1 Resources ...............................................................................................................................6
7.2 Competence ............................................................................................................................. 6
7.3 Awareness ..............................................................................................................................6
7.4 Communication ......................................................................................................................6
7.5 Documented information ................................................................................................... 6
7.5.1 General ...................................................................................................................... 6
7.5.2 Creating and updating ............................................................................................. 7
7.5.3 Control of documented information ....................................................................... 7
8Operation.............................................................................................................................................7
8.1 Operational planning and control ......................................................................................... 7
8.2 Information security risk assessment ................................................................................. 8
8.3 Information security risk treatment ..................................................................................8
9Performance evaluation .................................................................................................................8
9.1 Monitoring ,measurement , analysis and evaluation ...........................................................8
9.2 Internal audit ..........................................................................................................................8
9.2.1 General ......................................................................................................................8
9.2.2 Internal audit programme ................................................................................... 9
9.3 Management review ............................................................................................................... 9
9.3.1 General ...................................................................................................................9
9.3.2 Management review inputs ..................................................................................... 9
9.3.3 Management review results .................................................................................. 9
10 Improvement ................................................................................................................................. 10
10.1 Continual improvement ..................................................................................................... 10
10.2 Nonconformity and corrective action ........................................................................... 10
Annex A(normative)Information security controls reference ....................................................... 1
Bibliography ............................................................................................................................................... 19
OISO/IEC 2022-Allrightsreserved iii
摘要:
展开>>
收起<<
INTERNATIONALISO/IECSTANDARD27001Thirdedition2022-10Informationsecurity,cybersecurityandprivacyprotection—Informationsecuritymanagementsystems—RequirementsSécuritédeI'information,cybersécuritéetprotectiondelavieprivée—SystèmesdemanagementdelasécuritédeI'information—ExigencesReferencenumberISO/IEC270...
声明:如果您的权利被侵害,请联系我们的进行举报。
相关推荐
-
医疗器械设计开发控制指南VIP免费
 2024-04-12 351
2024-04-12 351 -
YY∕T 0664-2020医疗器械软件软件生存周期过程核查表VIP免费
 2024-04-12 365
2024-04-12 365 -
创新医疗器械注册申报流程

 2024-05-02 179
2024-05-02 179 -
20221028_医疗器械生产现场核查缺陷分析交流(江苏药省监局审核查验中心) (1)VIP免费
 2024-05-09 133
2024-05-09 133 -
医疗器械网络安全漏洞自评报告VIP专享
 2024-11-18 354
2024-11-18 354 -
内审检查表 MDR法规VIP免费
 2025-04-07 329
2025-04-07 329 -
07.产品风险管理报告VIP免费
 2025-09-12 91
2025-09-12 91 -
06.可用性确认报告或可用性总结性测试报告VIP免费
 2025-09-12 133
2025-09-12 133 -
特定上市前提交审查的质量管理体系信息-2025草案_中英文版VIP专享
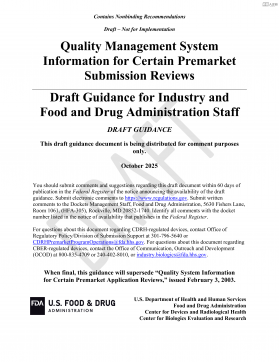
 2025-11-03 81
2025-11-03 81 -
医疗器械生产企业质量管理体系程序文件模板全套VIP免费
 2026-05-11 13
2026-05-11 13
作者:雨尘yc
分类:法规规范
价格:80质量币
属性:32 页
大小:472.59KB
格式:PDF
时间:2026-05-15